“Zero Trust Security Market is estimated to grow at a high CAGR during the forecast period 2024-2031.”
DataM Intelligence unveils exclusive insights into the Zero Trust Security Market 2026, highlighting emerging trends, growth drivers, and key regional opportunities worldwide. The report helps solve critical business challenges by identifying high-growth segments and reducing investment risks through actionable forecasts. With in-depth competitive benchmarking, it enables smarter strategies and confident decision-making.
Download your exclusive sample report today: (corporate email gets priority access):
https://www.datamintelligence.com/download-sample/zero-trust-security-market?prasad
United States: Recent Zero Trust Security Developments
✅ March 2026 – Federal agencies expand Zero Trust architecture implementation across cloud environments.
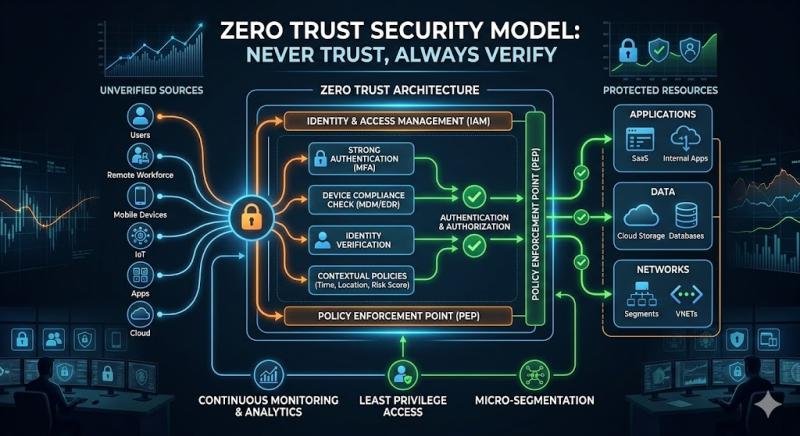
U.S. government departments continue rolling out Zero Trust frameworks under updated cybersecurity mandates, focusing on identity-based access controls and continuous verification. Agencies are strengthening protection for hybrid cloud systems and remote work infrastructures. Emphasis is placed on reducing lateral movement risks inside networks. This reflects a broader shift from perimeter-based to identity-centric security models.
✅ February 2026 – Major enterprises accelerate Zero Trust adoption for AI-driven workloads.
Large U.S. organizations are integrating Zero Trust security into AI and machine learning platforms to secure sensitive datasets and model pipelines. This includes stricter authentication, micro-segmentation, and real-time monitoring of access behavior. The approach is designed to prevent data leakage and unauthorized model manipulation. Adoption is rising across finance, healthcare, and tech sectors.
✅ January 2026 – Cloud providers enhance Zero Trust-native security toolkits.
Leading cloud platforms in the U.S. have expanded Zero Trust security features including adaptive authentication, device posture checks, and contextual access policies. These upgrades help enterprises enforce granular access controls across distributed environments. The focus is on securing APIs and multi-cloud workloads. This strengthens enterprise cloud security ecosystems.
✅ December 2025 – Defense and critical infrastructure sectors deepen Zero Trust integration.
U.S. defense agencies and critical infrastructure operators are implementing Zero Trust frameworks to protect against advanced persistent threats. Systems are being redesigned to assume breach and continuously validate users and devices. This improves resilience against cyberattacks targeting national infrastructure. It remains a key pillar of federal cybersecurity strategy.
Japan: Recent Zero Trust Security Developments
✅ March 2026 – Japanese government expands Zero Trust adoption in national digital infrastructure.
Japan is advancing Zero Trust security principles across government IT systems as part of its broader digital transformation strategy. Agencies are prioritizing identity verification, encrypted communications, and least-privilege access models. The initiative aims to improve resilience against growing cyber threats. This supports secure modernization of public sector infrastructure.
✅ February 2026 – Financial institutions accelerate Zero Trust deployment.
Major Japanese banks and financial service providers are strengthening cybersecurity frameworks using Zero Trust models. Focus areas include secure customer authentication, fraud prevention, and continuous risk evaluation. Institutions are also integrating behavioral analytics for anomaly detection. This enhances trust in digital banking ecosystems.
✅ January 2026 – Telecom operators integrate Zero Trust for 5G and edge networks.
Japanese telecom companies are embedding Zero Trust security into 5G and edge computing environments. This includes micro-segmentation and device-level authentication for connected devices. The approach helps secure massive IoT and industrial connectivity ecosystems. It supports safer rollout of next-generation networks.
✅ December 2025 – Industrial and manufacturing sectors adopt Zero Trust for OT systems.
Japanese manufacturers are increasingly applying Zero Trust principles to operational technology (OT) and smart factory environments. This includes restricting device-to-device communication and enforcing strict identity validation. The goal is to reduce cyber risks in highly automated production systems. It strengthens cybersecurity in Industry 4.0 environments.
Zero Trust Security Market: Drivers
Zero Trust Security is gaining rapid adoption as cyber threats grow more sophisticated and distributed. Enterprises are shifting from perimeter-based models to identity-centric security frameworks. Regulatory compliance and data protection mandates are driving enterprise-wide implementation. Cloud adoption and remote work are accelerating demand for robust access controls. This creates long-term opportunities for scalable cybersecurity platforms and recurring revenue models.
Get Customization in the report as per your requirements:
https://www.datamintelligence.com/customize/zero-trust-security-market?prasad
Zero Trust Security Market: Major Players
IBM Corporation, Akamai Technologies, Palo Alto Networks, Cisco Systems, Inc., Trend Micro Incorporated, Okta, Broadcom, VMware, Inc., FireEye, and Check Point Software Technologies Ltd.
The Zero Trust Security Market is expanding rapidly as enterprises accelerate digital transformation and strengthen cyber resilience, driven by leading cybersecurity and technology providers such as IBM Corporation, Akamai Technologies, Palo Alto Networks, Cisco Systems, Inc., and Trend Micro Incorporated. These organizations are advancing identity-centric security frameworks, continuous verification models, and AI-driven threat detection systems that are redefining enterprise security architectures. Their solutions are helping organizations reduce attack surfaces, secure hybrid cloud environments, and protect sensitive data across increasingly distributed digital ecosystems. This report provides actionable insights that help these companies align with evolving regulatory requirements, cyber threat landscapes, and enterprise security priorities, strengthening their strategic positioning within the Zero Trust Security Market.
At an ecosystem level, companies such as Okta, Broadcom, VMware, Inc., FireEye, and Check Point Software Technologies Ltd. complement core security infrastructure providers by enabling identity management, endpoint protection, network virtualization, and threat intelligence capabilities. These companies contribute critical components of a Zero Trust architecture, including continuous authentication, micro-segmentation, and real-time threat monitoring. Their combined expertise ensures layered security across endpoints, networks, applications, and cloud environments, significantly improving organizational cyber defense posture. The synergy between platform providers and specialized cybersecurity firms is accelerating adoption and maturity of Zero Trust frameworks across industries.
Buy Now & Unlock 360° Market Intelligence:
https://www.datamintelligence.com/buy-now-page?report=zero-trust-security-market
Segment Covered in the Zero Trust Security Market:
By Authentication Type
The market is segmented into multi-factor authentication (MFA) 65% and single-factor authentication (SFA) 35%, with MFA dominating due to its enhanced security through multiple verification layers such as biometrics, OTPs, and tokens. SFA remains in use for basic access systems but is gradually declining due to security vulnerabilities. Rising cyber threats and regulatory compliance requirements are driving strong adoption of MFA solutions.
By Solution Type
Solutions include network security 20%, data security 18%, endpoint security 15%, security analytics 12%, security orchestration automation and response (SOAR) 10%, API security 10%, security policy management 8%, and others 7%, with network and data security dominating due to the need to protect enterprise infrastructure and sensitive information. Endpoint security is growing with increasing remote work trends. Security analytics and SOAR solutions are gaining traction with real-time threat detection and response capabilities. Expanding cybersecurity landscape drives demand across all segments.
By End-User
End-users include IT and telecom 25%, BFSI 20%, government 15%, healthcare 10%, manufacturing 10%, retail 10%, energy and power 5%, and others 5%, with IT and telecom dominating due to high exposure to cyber threats and need for advanced security solutions. BFSI and government sectors also represent significant demand due to sensitive data handling. Healthcare and manufacturing sectors are increasingly adopting cybersecurity solutions with digital transformation. Rising cyber risks across industries support market growth.
Regional Analysis
North America – 35% Share
North America leads with 35% share driven by strong cybersecurity adoption in the United States and Canada. MFA dominates authentication type. Network and data security solutions lead. IT & telecom and BFSI sectors are primary end-users. Presence of major cybersecurity companies supports market growth.
Europe – 25% Share
Europe holds 25% share due to stringent data protection regulations in Germany, the UK, and France. MFA adoption is high. Data security and endpoint security solutions dominate. BFSI and government sectors lead demand. Regulatory frameworks such as GDPR drive market expansion.
Asia Pacific – 20% Share
Asia Pacific accounts for 20% share with rapid digitalization in China, India, Japan, and South Korea. MFA adoption is growing. Network and endpoint security solutions dominate. IT & telecom and manufacturing sectors lead. Increasing cyber threats drive demand.
Latin America – 10% Share
Latin America holds 10% share with growing cybersecurity adoption in Brazil and Mexico. MFA is widely used. Network and data security solutions dominate. BFSI and government sectors lead. Expanding digital infrastructure supports growth.
Middle East & Africa – 10% Share
The Middle East and Africa region records 10% share driven by adoption in the UAE, Saudi Arabia, and South Africa. MFA dominates authentication. Network and endpoint security solutions lead. Government and energy sectors are key end-users. Increasing investments in cybersecurity support regional development.
Most Frequently Asked Questions in the Zero Trust Security Market Research Industry:
➠ Who leads the Zero Trust Security industry and what’s their competitive positioning regarding capacity, performance, and profitability?
➠ What growth opportunities and market challenges do Zero Trust Security market vendors face?
➠ Which segments show the highest growth potential and market share distribution?
➠ What factors are driving or limiting Zero Trust Security market growth?
➠ What are the dominant sales and distribution strategies in the Zero Trust Security industry?
Request for 2 Days FREE Trial Access:
https://www.datamintelligence.com/reports-subscription?prasad
✅ Competitive Landscape
✅ Technology Roadmap Analysis
✅ Sustainability Impact Analysis
✅ KOL / Stakeholder Insights
✅ Consumer Behavior & Demand Analysis
✅ Import-Export Data Monitoring
✅ Live Market & Pricing Trends
Have a look at our Subscription Dashboard:
https://www.youtube.com/watch?v=x5oEiqEqTWg
Contact Us –
Company Name: DataM Intelligence
Contact Person: Sai Kiran
Email: Sai.k@datamintelligence.com
Phone: +1 877 441 4866
Website: https://www.datamintelligence.com
About Us –
DataM Intelligence is a Market Research and Consulting firm that provides end-to-end business solutions to organizations from Research to Consulting. We, at DataM Intelligence, leverage our top trademark trends, insights and developments to emancipate swift and astute solutions to clients like you. We encompass a multitude of syndicate reports and customized reports with a robust methodology.
Our research database features countless statistics and in-depth analyses across a wide range of 6300+ reports in 40+ domains creating business solutions for more than 200+ companies across 50+ countries; catering to the key business research needs that influence the growth trajectory of our vast clientele.
This release was published on openPR.